Many small business owners believe they are too small to be hacked. In reality, they are the victims of more than 28% of data breaches (Source: StrongDM).
Bottom line, no one is immune from a cyber incident…and the statistics are startling:
- $4.62m (USD) average cost of data breach involving ransomware (Source: IBM Cost of Data Breach 2021)
- 79% of organizations expect ransomware attacks this year (Source: Security Magazine, May 2023)
- Cybercrime is expected to inflict annual damages of $10.5 trillion by 2025 (Source: StrongDM)
- The average impact from ransomware attacks cost one month of recovery time, negatively affected the business’s ability to operate, and caused 86% to lose business and/or revenue. (Source: Sophos’ State of Ransomware 2022)
In early June 2023, the Russian hacker group Clop exploited security flaws in the widely used MOVEitTransfer tool to launch a massive cyberattack, targeting the Louisiana and Oregon Offices of Motor Vehicles, Aon, Allianz, the BBC, British Airways, and numerous federal agencies and universities. The subsequent enormous theft of personal data demonstrates the immediate need for businesses to prepare their systems to handle security breaches.
Providing Value as a Trusted Advisor
This is where you come in as a trusted advisor, a risk consultant who educates clients on cyber risk management.
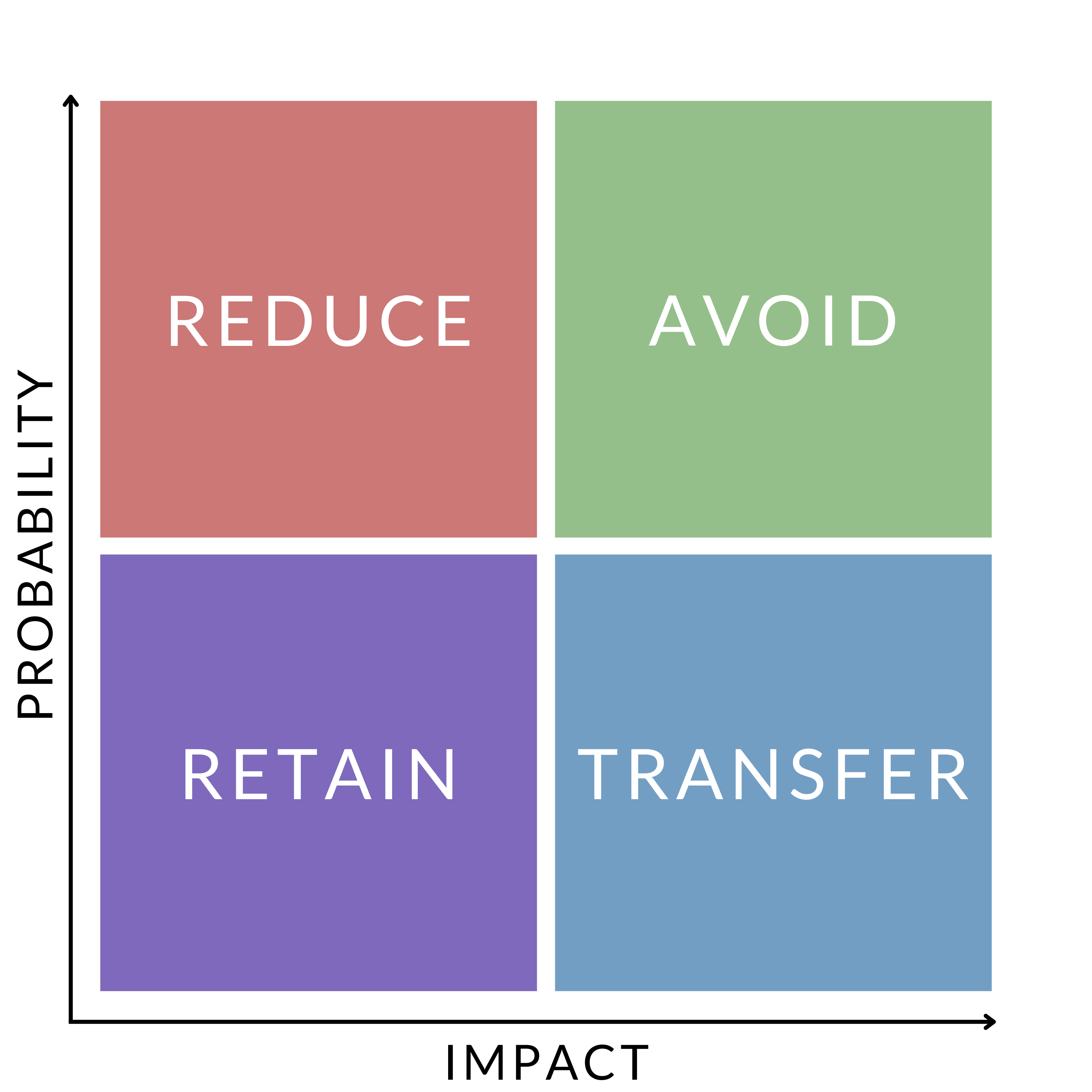
Consider the risk decision matrix, then ask yourself:
- How can my clients proactively prepare before an attack even happens? (avoid)
- How can I help my clients reduce their cyber risk?
When a business fails to reduce its cyber risk, it jeopardizes its business continuity and reputation in the event of a breach. Very few small and mid-size businesses have the necessary resources to recover from a cyberattack.
However, like any risk, the threat of a cyberattack can be managed for any size or type of organization, using the five-step risk management process: 1) Identify, 2) Analyze, 3) Evaluate, 4) Implement, 5) Monitor.
